Catching Unauthorized VPN Access in Under 60 Seconds
Early this morning, a suspicious login was detected on a Google Workspace account belonging to one of my clients. The login came through a commercial VPN (Mullvad, to be specific) which immediately triggered a security signal.
The Huntress SOC team caught it the moment the session was initiated. Within approximately 40 seconds, including the alert firing and a human analyst reviewing it to rule out a false positive. The account’s access was already revoked to prevent any further damage.
Less than one minute. That’s real-time incident response.
How it unfolded
The event log tells the full story. At 01:06:31 UTC+1, a login was performed from a Swiss hosting IP. Within the same second, the login was verified and marked successful.
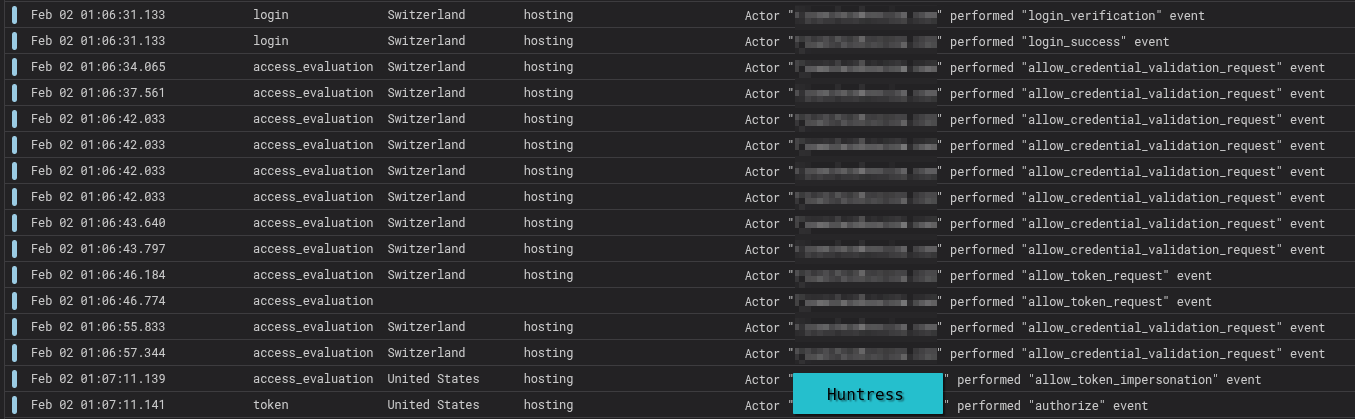
By 01:07:11, the SOC analysts had already contained it (that’s the last two logs, from their datacenter)
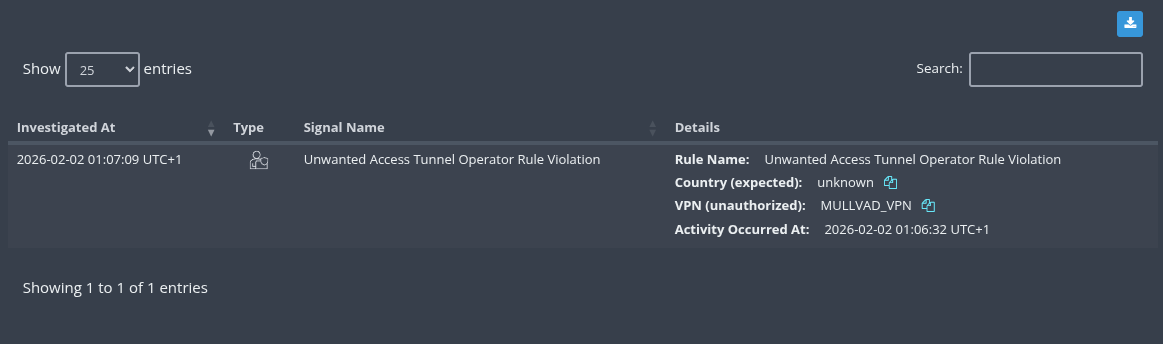
The security signal was a simple VPN access: Unwanted Access Tunnel Operator Rule Violation. The VPN provider (Mullvad VPN) was identified as unauthorized, as it wasn’t on the allowed list for that specific customer.
Why was the response so fast?
Credit where it’s due: Google has significantly improved the speed at which it delivers Workspace audit logs. On average, logs are now available within one second of the event occurring. This basically means real time telemetry gives any connected SOC an enormous advantage in response time. For reference, Microsoft 365 audit logs typically take a bit longer to reach any SIEM (around 5 to 7 minutes on average).
Combined with Huntress’s 24/7 SOC coverage, this creates a detection-to-response pipeline that’s measured in seconds, not hours.
What actually happened
In this particular case, the story had a mundane ending: it was a legitimate user logging in from their personal computer, which happened to have a VPN active. Not an actual breach, but the alert was absolutely correct to fire. The access came from outside the expected parameters (source and time), and until proven otherwise, it had to be treated as a threat.
This is exactly how identity security should work.
The questions you should be asking
This incident, despites ending up being benign, raises critical questions that every organization should be able to answer:
-
Do you allow users to access sensitive data from personal devices? If so, you’re trusting machines you don’t control with your company’s most critical assets.
-
Could you guarantee business continuity if an attacker stole browser cookies or session tokens from an unmanaged device? Cookie theft effectively bypasses MFA entirely. The attacker walks into a pre-authenticated session, no questions asked.
-
Do you have identity protection in place? Controls that detect cookie/token theft or users handing over their MFA codes to a phishing page are not optional anymore.
-
Could you determine the blast radius of a cloud incident? If someone gains access to your Google Workspace or Microsoft 365 tenant, can you tell which files were accessed or downloaded?
-
Do you have a disaster plan? Within one minute, not a lot of damage can be done, but it can still hurt. Backups are mandatory, as the cloud does not have them included by default (unless explicitly purchased).
If any of these questions make you uneasy, that’s a healthy reaction. Identity is the first line of battle in modern cybersecurity. Once an attacker gains access to an account, they’re inside the kingdom.
The takeaway
Monitoring identity is no longer a nice-to-have. Between token theft, session hijacking, phishing-resistant MFA bypass techniques, and the sheer volume of cloud-based collaboration, your accounts are the perimeter now.
Having a SOC that operates in real-time, with the right tooling and the right telemetry, turns what could be a devastating breach at midnight into a 40-second non-harmful event.
If you want to improve your organization’s identity security posture, get in touch with me. I’m here to help, not to judge. Every company has gaps, and the important thing is to start closing them.
And to close on a personal note: